Self-Developed Custody Stack
We operates on a proprietary custody infrastructure built specifically for structured digital wealth preservation. The stack integrates cold storage systems, access governance controls, and multi-layer security architecture within a unified framework.
By designing and maintaining its own custodial environment, KayNexa reduces dependency on third-party custody risk while strengthening operational oversight. Each layer of the stack is engineered to minimize exposure, protect private key integrity, and enforce disciplined authorization protocols. This self-developed architecture ensures that security is not an add-on feature, but the foundation of the Vault itself.

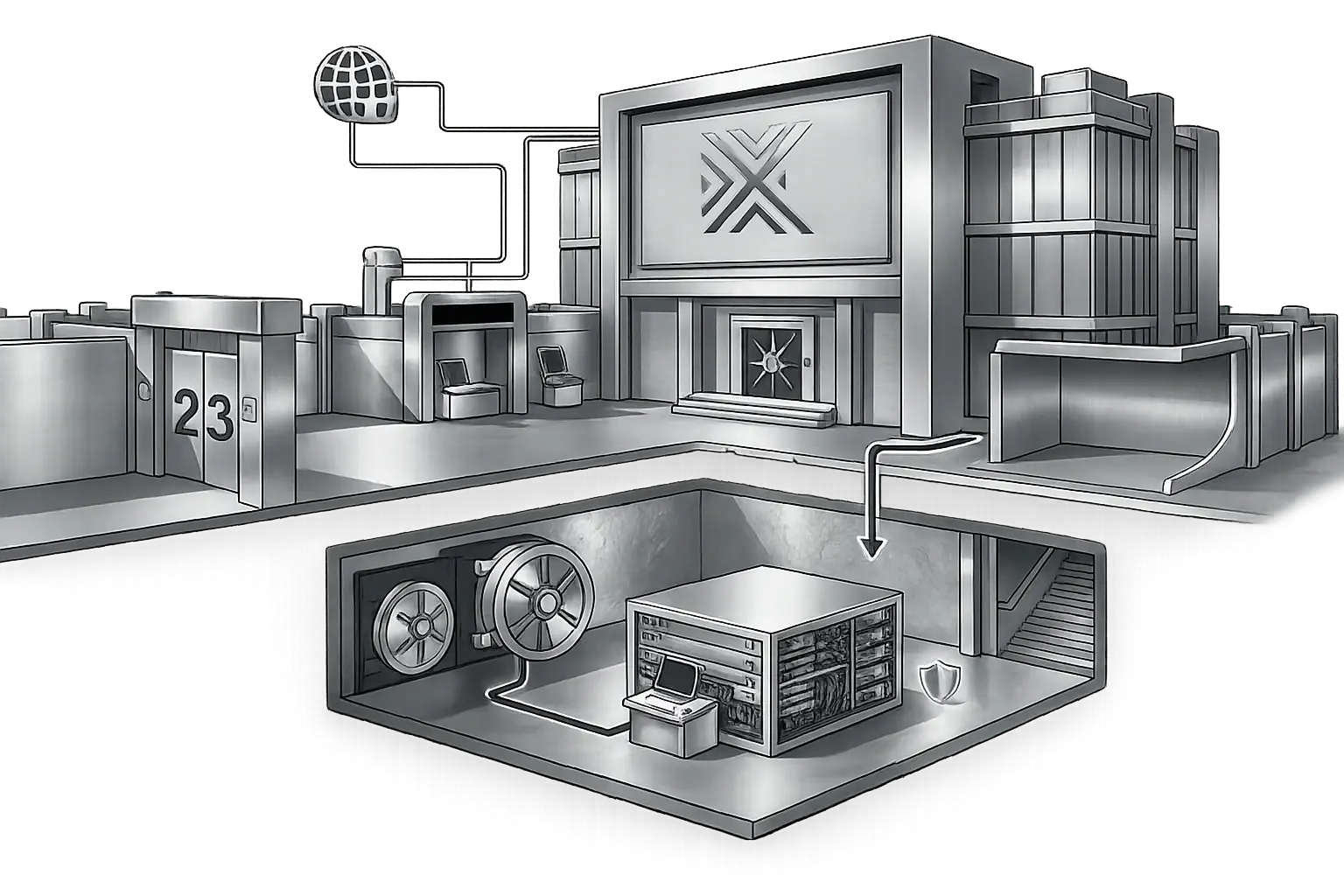
Cold Storage Architecture
The majority of digital assets held within the Vault are secured through a dedicated cold storage architecture,, isolated from continuous online exposure and protected within controlled environments.
Private key material is managed through structured custody protocols, reducing vulnerability to external threats while maintaining operational integrity. Access layers are governed by authorization frameworks designed to prevent unauthorized movement of capital. This architecture ensures that digital wealth remains insulated from unnecessary risk, combining offline protection with disciplined oversight to preserve long-term capital stability.
Multi-Layer Firewall Infrastructure
We deployed a multi-layer firewall infrastructure designed to monitor, filter, and restrict unauthorized network activity across custodial systems. Each layer reinforces perimeter security, reducing exposure to intrusion attempts and strengthening overall operational resilience.
Network segmentation and layered defense protocols ensure that critical custody components remain isolated from external threats. Continuous monitoring systems detect anomalies in real time, enabling rapid response while maintaining institutional-grade protection standards.


Access Governance & Withdrawal Controls
The Vault operates under strict access governance protocols to ensure that custodial systems remain controlled and accountable. Role-based permissions, multi-layer authorization, and operational separation of duties reduce internal and external risk exposure.
Withdrawal requests are processed through structured approval workflows designed to prevent unauthorized asset movement. Each transaction passes defined verification layers, maintaining security integrity while preserving disciplined oversight of capital transfers.
Monitoring & Incident Response Framework.
We operates continuous system monitoring across its custodial infrastructure, tracking network activity, access behavior, and transactional integrity in real time. Automated alerts and internal oversight mechanisms detect anomalies before they escalate into operational threats.
In the event of a security event, predefined incident response protocols are activated immediately. Escalation procedures, containment controls, and system audits ensure that risks are addressed swiftly while maintaining stability and custody integrity.


